
There is No Single Roadmap
Here’s a very common misconception for beginners in the fields of technology: There is a single roadmap that you should follow in order to become successful or get a good job and not become the average Joe. This “single” roadmap differs so widely between people and subfields of the tech industry, that you can’t even find THE roadmap everyone is ...
Variadic Functions & stdarg.h
If you’ve ever programmed using C or C++, you’ve probably come across the function printf(). It’s a very popular function and all of C/C++ coders have seen it before.
printf (short for print formatted) basically prints formatted data to standard output (STDOUT). The function does so by using its format parameter, and the variables you want to p...
Catch the IEX if You Can: PowerShell Deobfuscation
A lot of the time when working with malware or when investigating an incident, you may encounter PowerShell executing obfuscated commands which may look like gibberish.

Reverse Engineering Writeup: ASCWG Finals 2020
Arab Security Cyber Wargames Finals 2020 was held on September 12th in Nile Ritz Cairo.
Photo Credit: Arab Security Conference.
This time I was the author of three of the five challenges presented in the finals. Here are the writeups for them.
Who Moved My Cheese?
We’ve all seen how 2020 is a very different year compared to the years of the last decade.
Even after things get back to “normal”, they just won’t be the same. That is due to a lot of changing factors around us that we can’t directly control such as the economy, the political scenes, and a lot of others. We’re unable to predict what will happen...
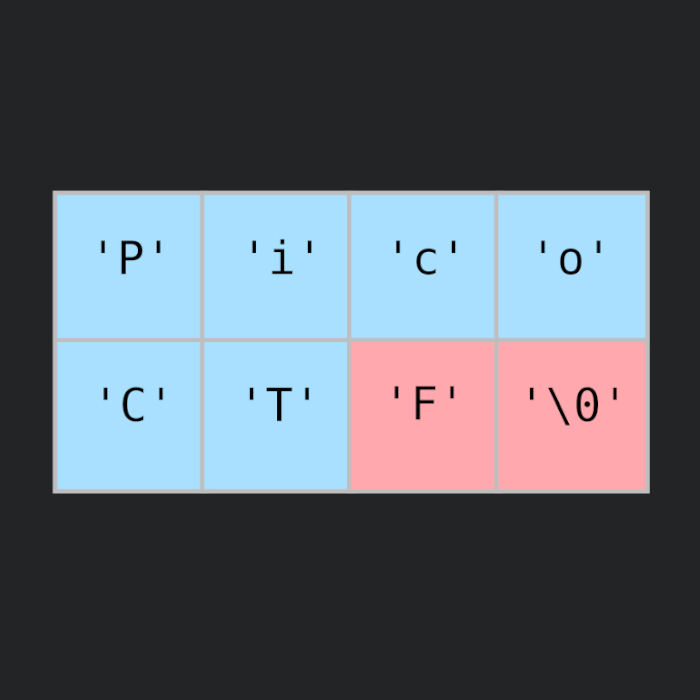
Buffer Overflows: PicoCTF2018-BufferOverflow-1
I wrote this post back in late May 2019 but hadn’t published it and I don’t really remember why I didn’t. It was supposed to be a follow up for the post on the buffer overflow basics.
Anyway since I’ve already written it, here it is.

IdeaPad 3XX (Realtek): Fixing the WiFi dropping on Linux
The IdeaPad 310 (specifically) is a horrible laptop, the keyboard layout was designed by a person whom I can almost swear has never used a keyboard before and the build is extremely cheap. I mean, come on, who places the shift key right next to the arrow key LIKE THIS.

EG-CERT Writeup: EG-CTF Finals 2019
EG-CTF Finals 2019 was held on December 4th in EIEC, New Cairo at ICT 2019’s venue.
The challenges were extremely fun and challenging and I learned A LOT during the CTF.
36 post articles, 5 pages.