The first blog post I ever posted here was on 7 Dec. 2018. However, my story with writing goes way beyond that. If you’re not interested in the story, you can skip to “But, why?”. In the other half of this post, I talk about why I started this blog, what I gained from it, and why you may want to do the same.
Backstory
The whole story started with me writing in high school on small Facebook groups for some friends and acquaintances with mutual interests. Short posts such as games and comic reviews. A while after that, I joined Big Geeks (🫡R.I.P.) and started writing more on similar (but more technical) topics such as more comic books and videogames, computer hardware, the tech industry, etc…. At the time, it was just a side thing I was doing besides school.
Fast forward to the last year of high school, after Big Geeks weren’t that active anymore, I went back to writing for my circle on Facebook at the time (not just in groups) in the form of Notes*. My circle at the time included a lot of like-minded people, so the notes would initiate lots of interesting (mostly civil) discussions. I used to write anything from comic book discussions to technical articles like Linux distro reviews. I did that for a while until my second year of university. At this point, I decided to start this blog for, mainly, knowledge sharing and organising my posts better. I also enjoyed writing as it made me relax. So, that did also benefit me. However, it wasn’t the only benefit!
*Back in the day, Facebook had a feature where you could write notes on your profile and people could read them. They would be published as a post the first time but they would be kept as a section on your profile so that anyone could go back to them.
Facebook Notes
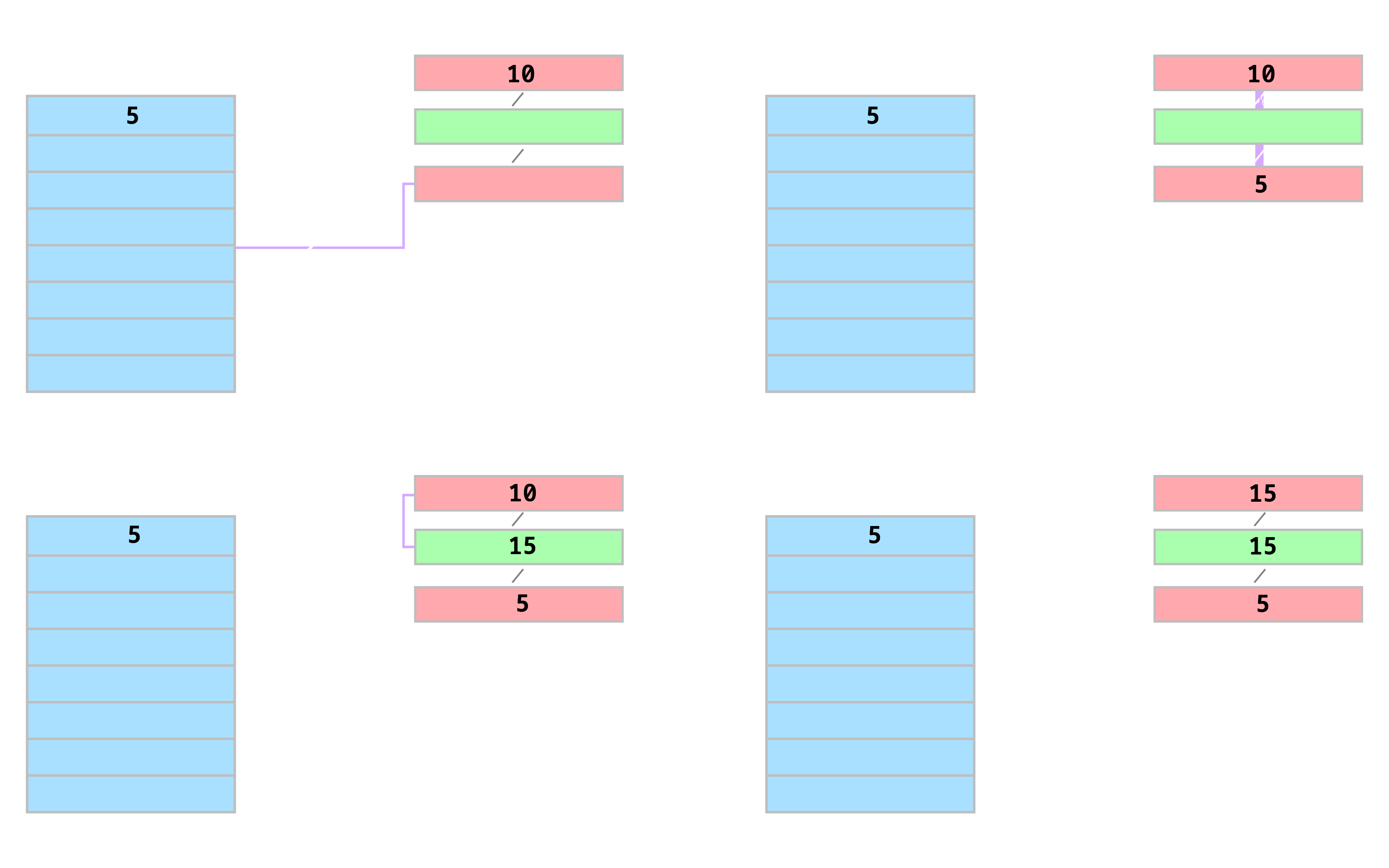
Unfortunately, Facebook doesn’t have that feature anymore. I also (fortunately) no longer use Facebook. So, I can’t get any of the original notes I posted from Facebook. However, I dug deep in my drives and found a file which contained a draft of one of my early notes :) Sharing it here just for completeness.
As you can see, it was more of a note that was supposed to start a discussion. Needless to say, I did not really know much about the tech industry at the time. I just had some hopes and dreams, a bit of technical knowledge, and the will to communicate them. In my defence, I was in high school, ha!
satharus.wordpress.com
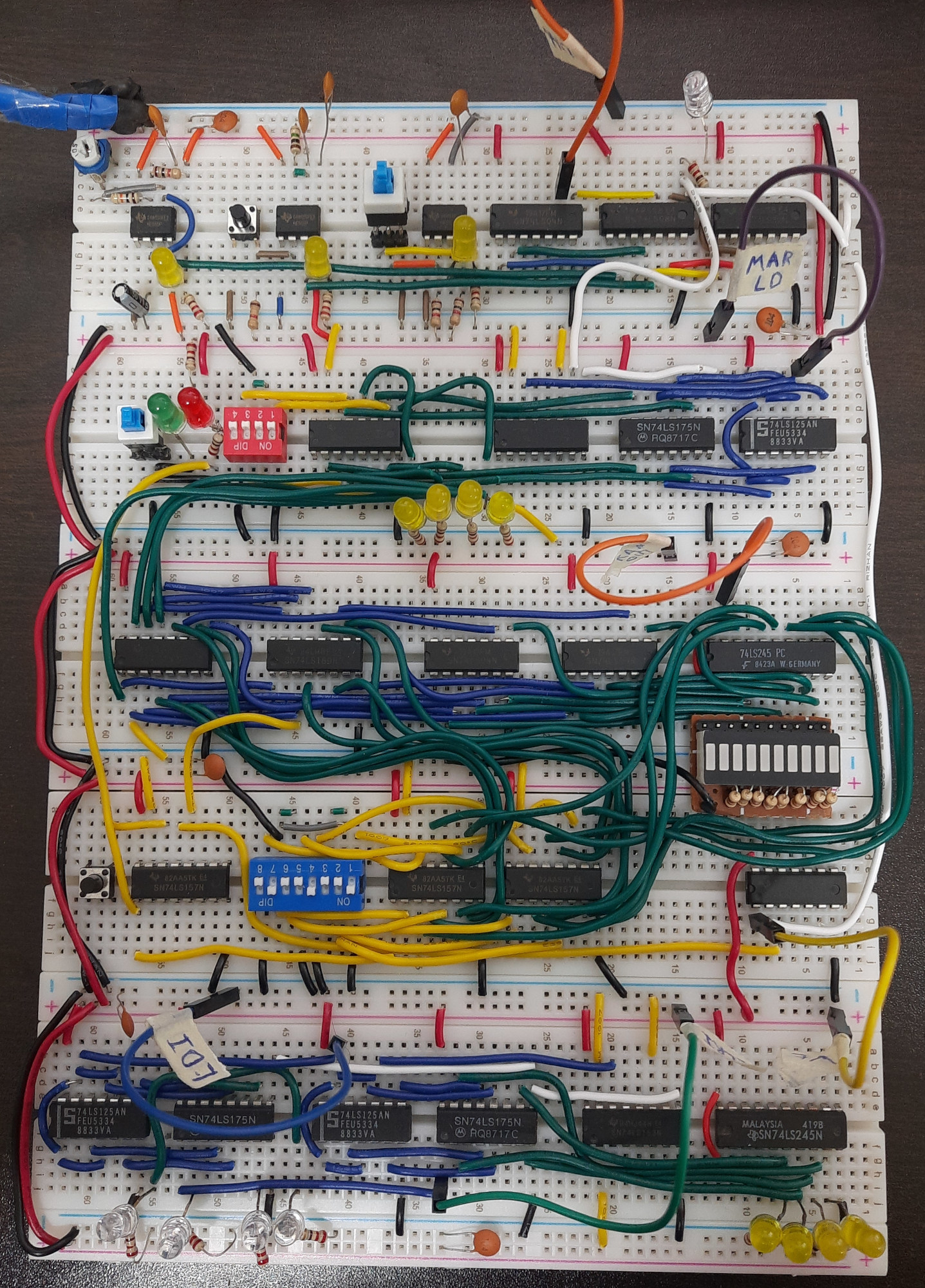
At first, I started the blog on WordPress using the first template I could find. However, throughout the years and after many different iterations, themes, and names: Satharus’ not-so-secret diary, Satharus’ Blog, and finally, Blog of Satharus, I moved to GitHub Pages for a more reader-friendly experience with no forced tracking. At that point, I gave it the name “Technoir”. This is the current version of “Technoir - Blog of Satharus” which I plan on keeping.
A small piece of trivia, “Satharus” was the name of my character in a couple of RPG games during high school and it just kinda stuck with me. It doesn’t mean anything and I literally got it from a random name generator in World of Warcraft.
But, why?
Why not? It is fun.
In all seriousness, though, I started this blog and continue to write for many reasons:
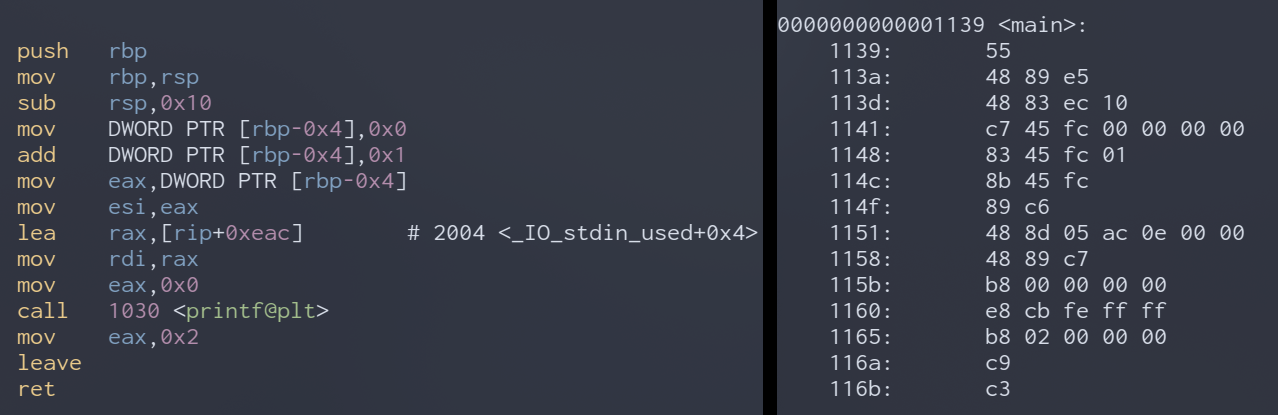
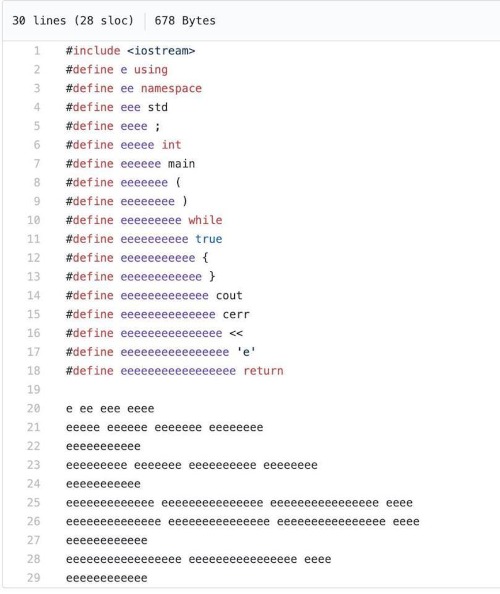
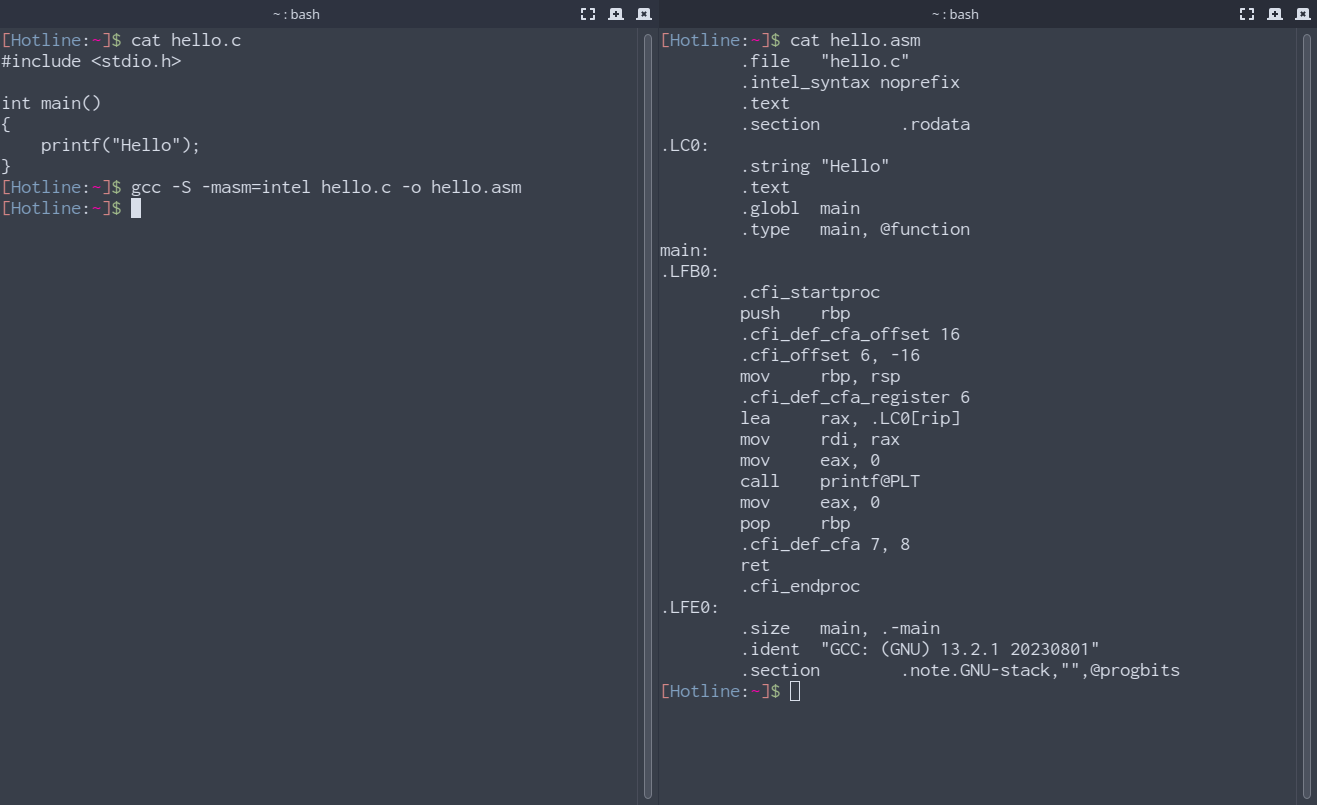
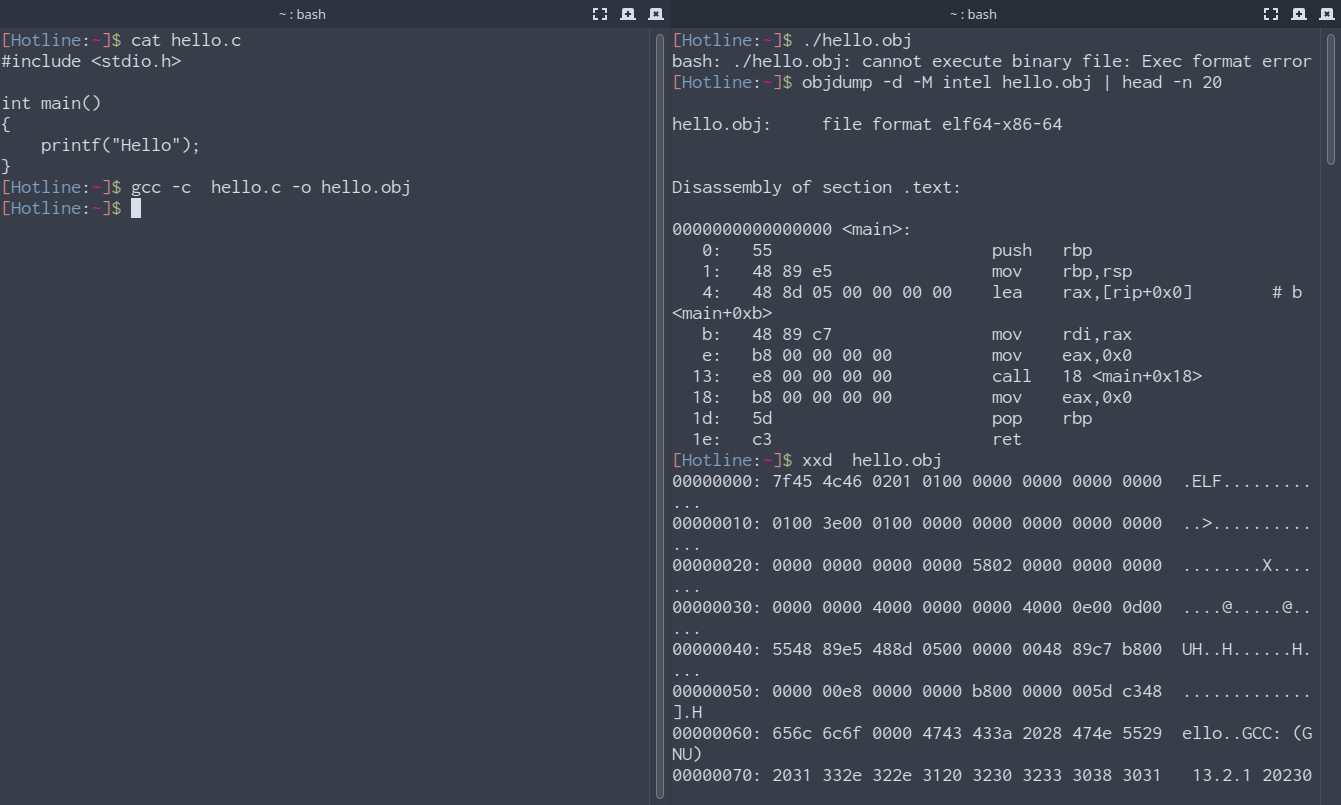
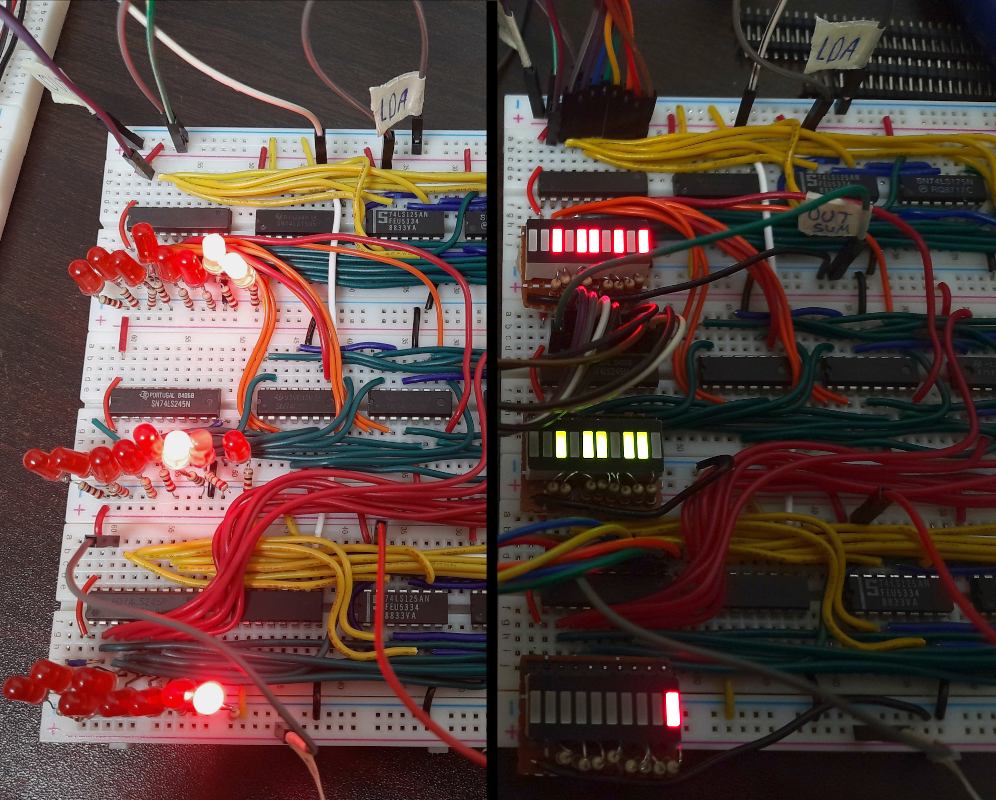
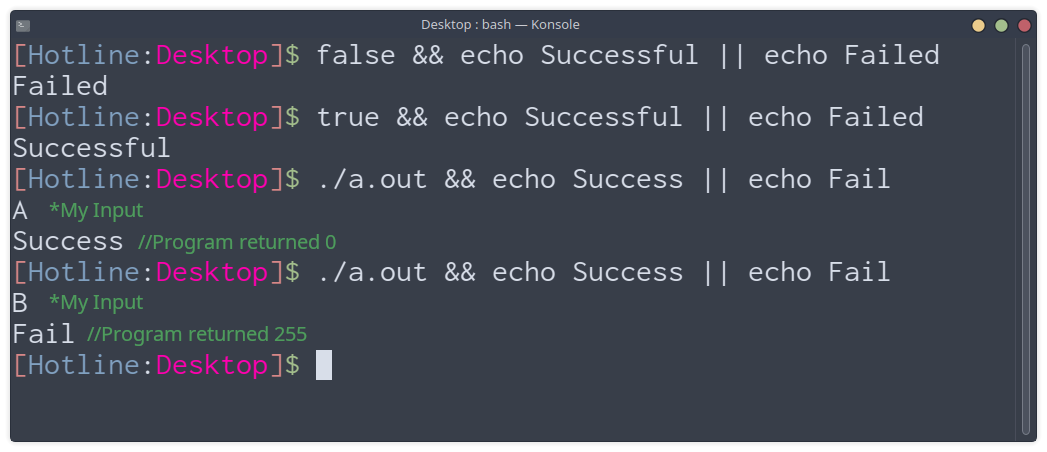
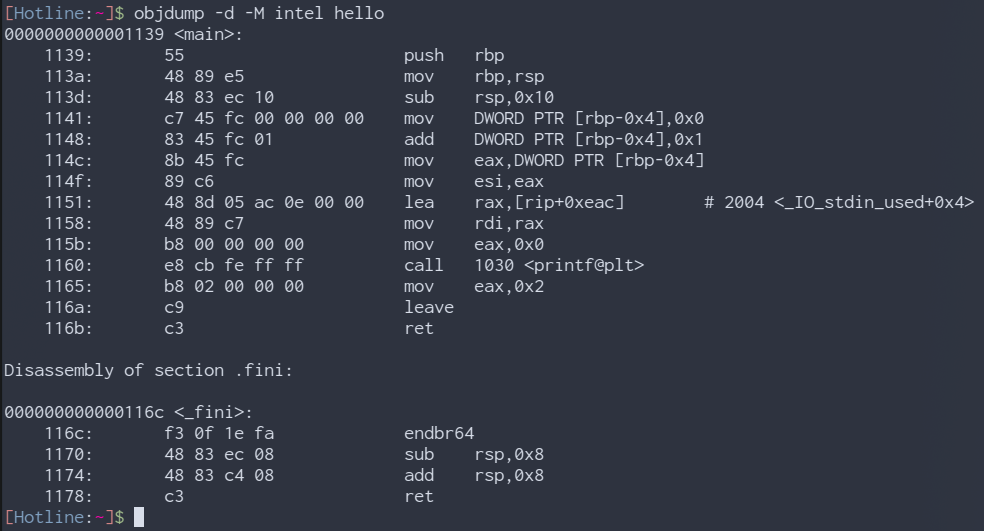
Knowledge Sharing
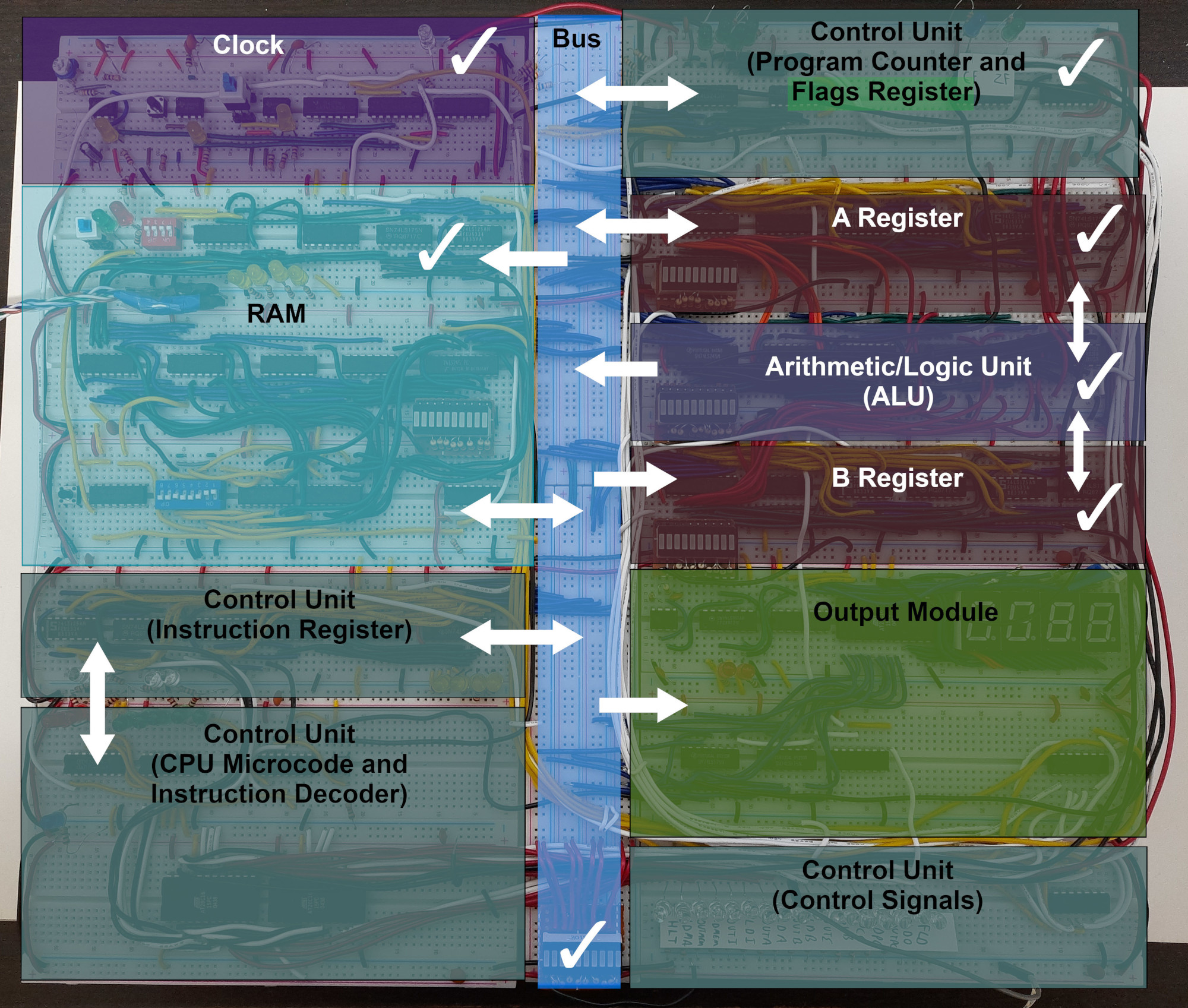
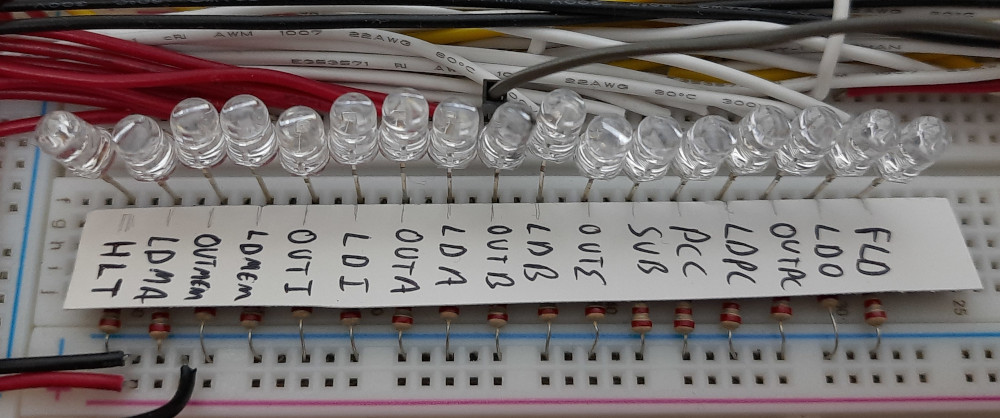
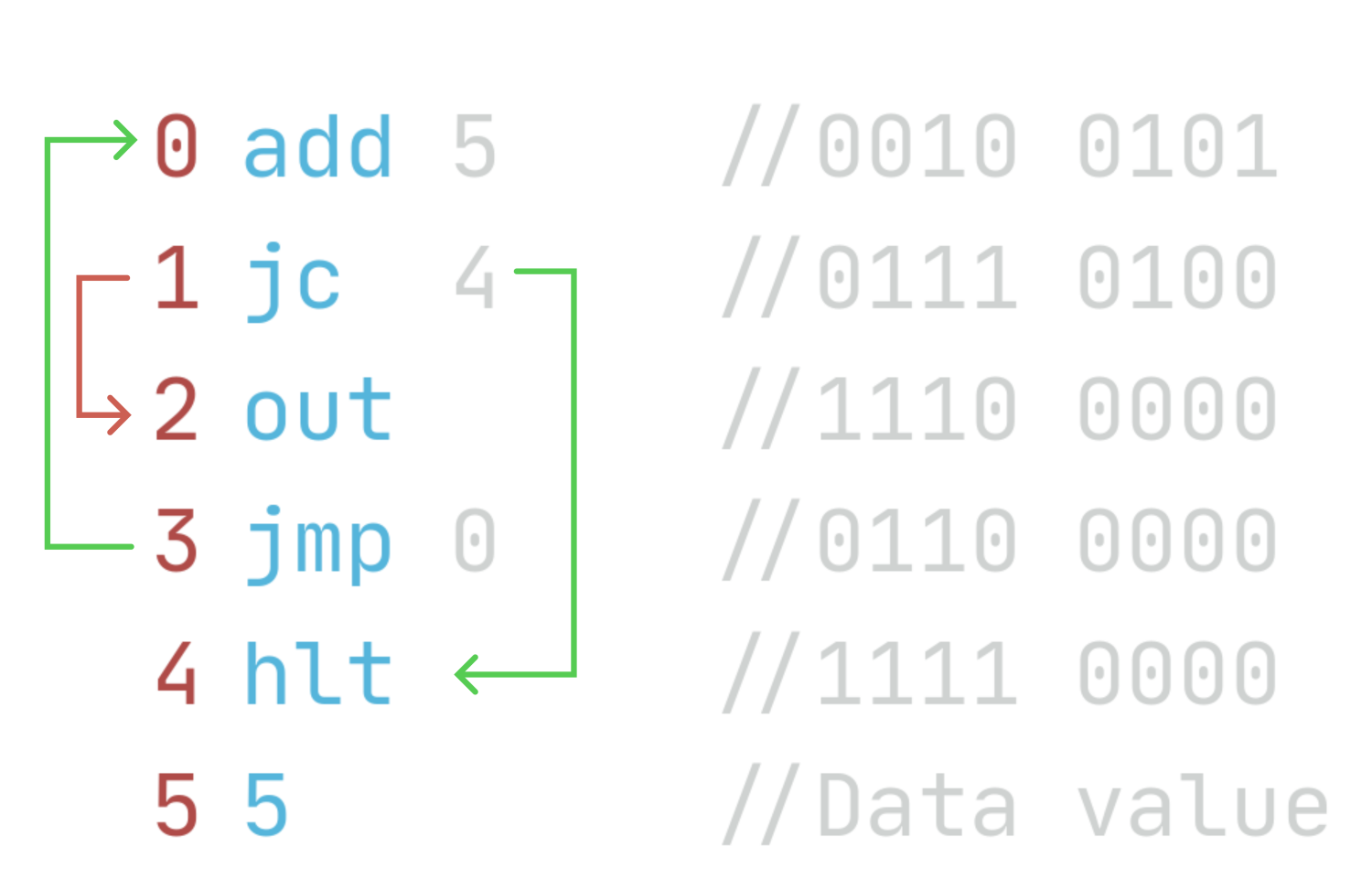
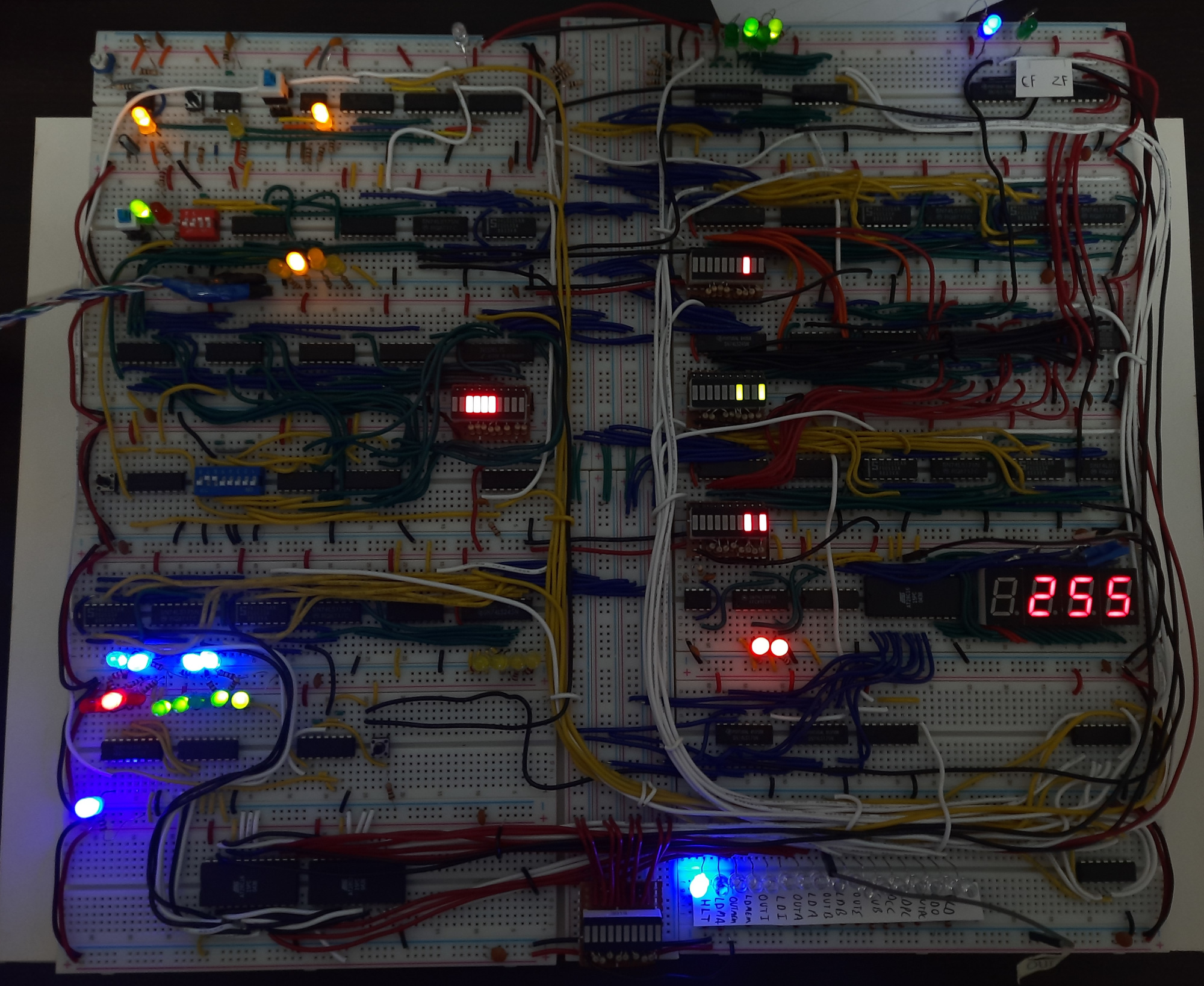
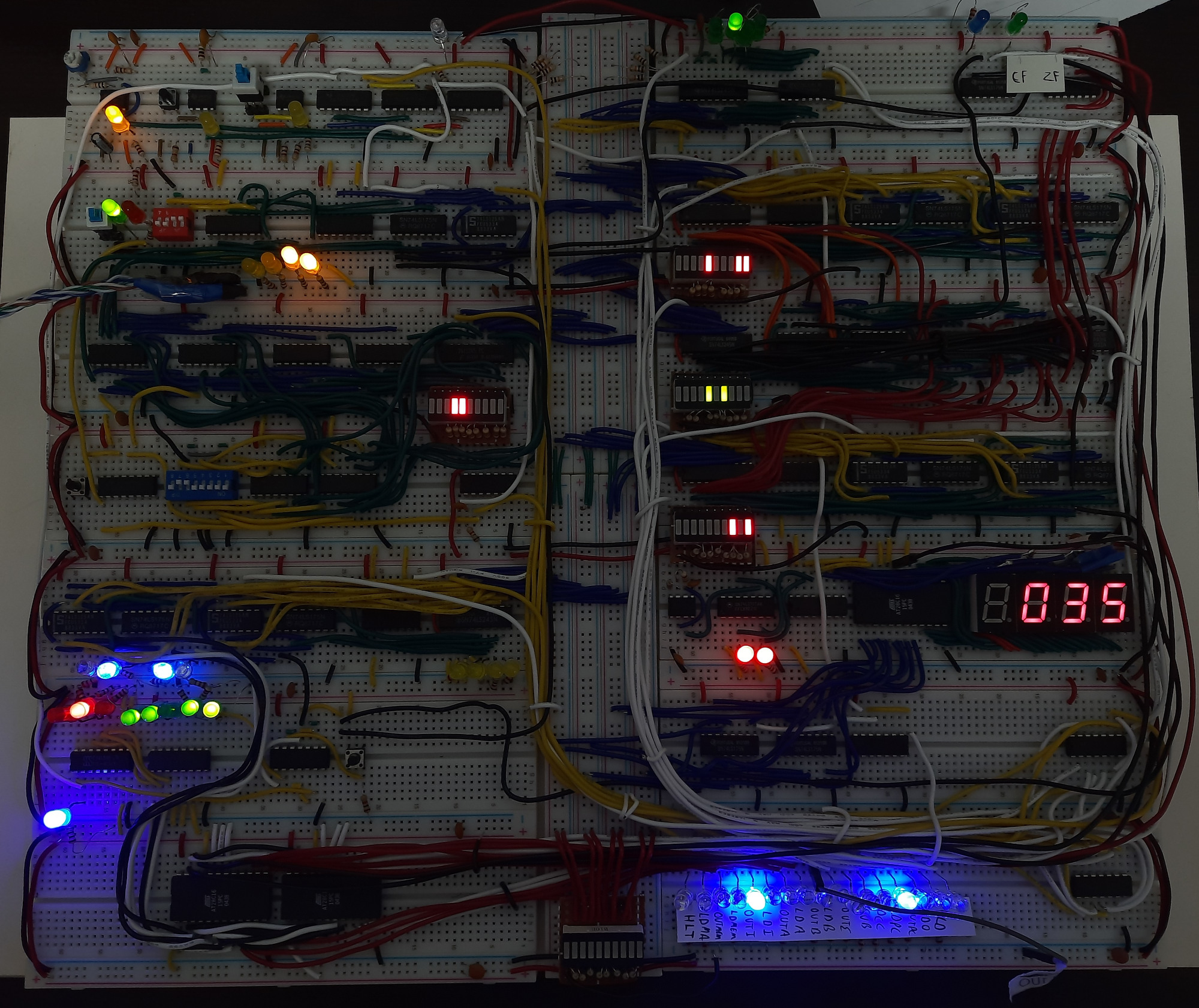
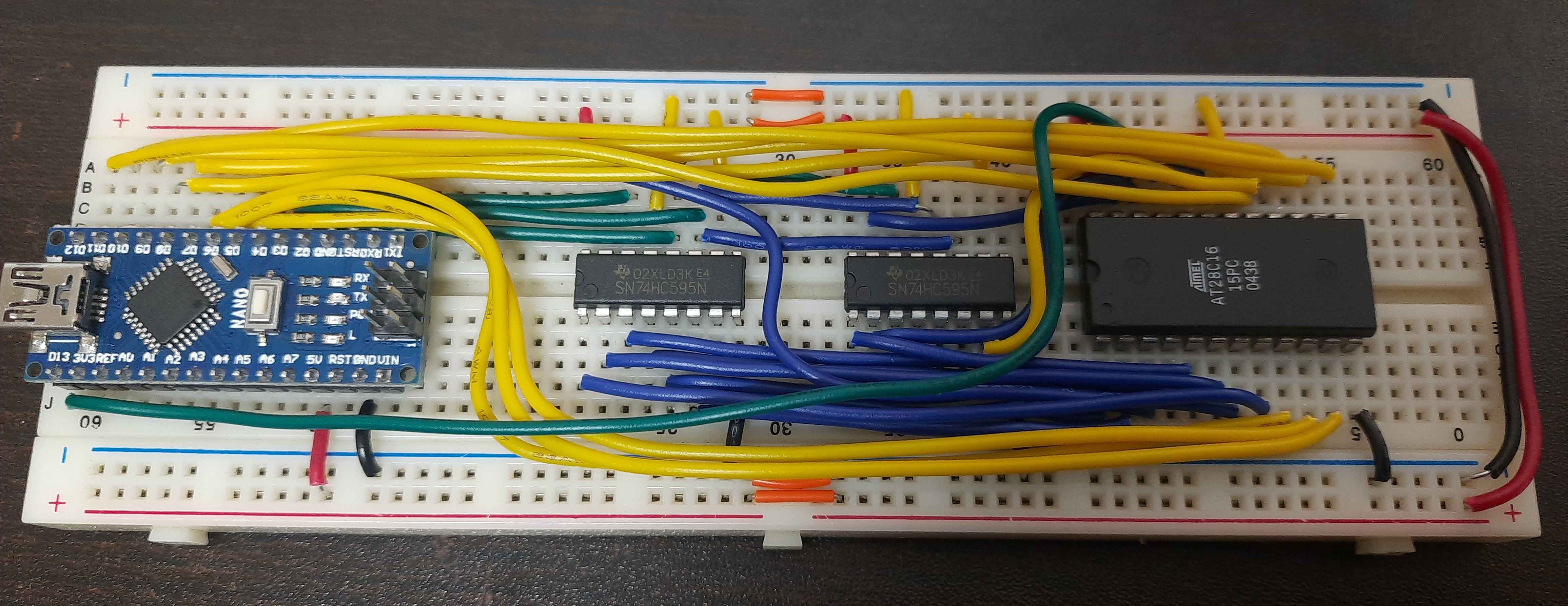
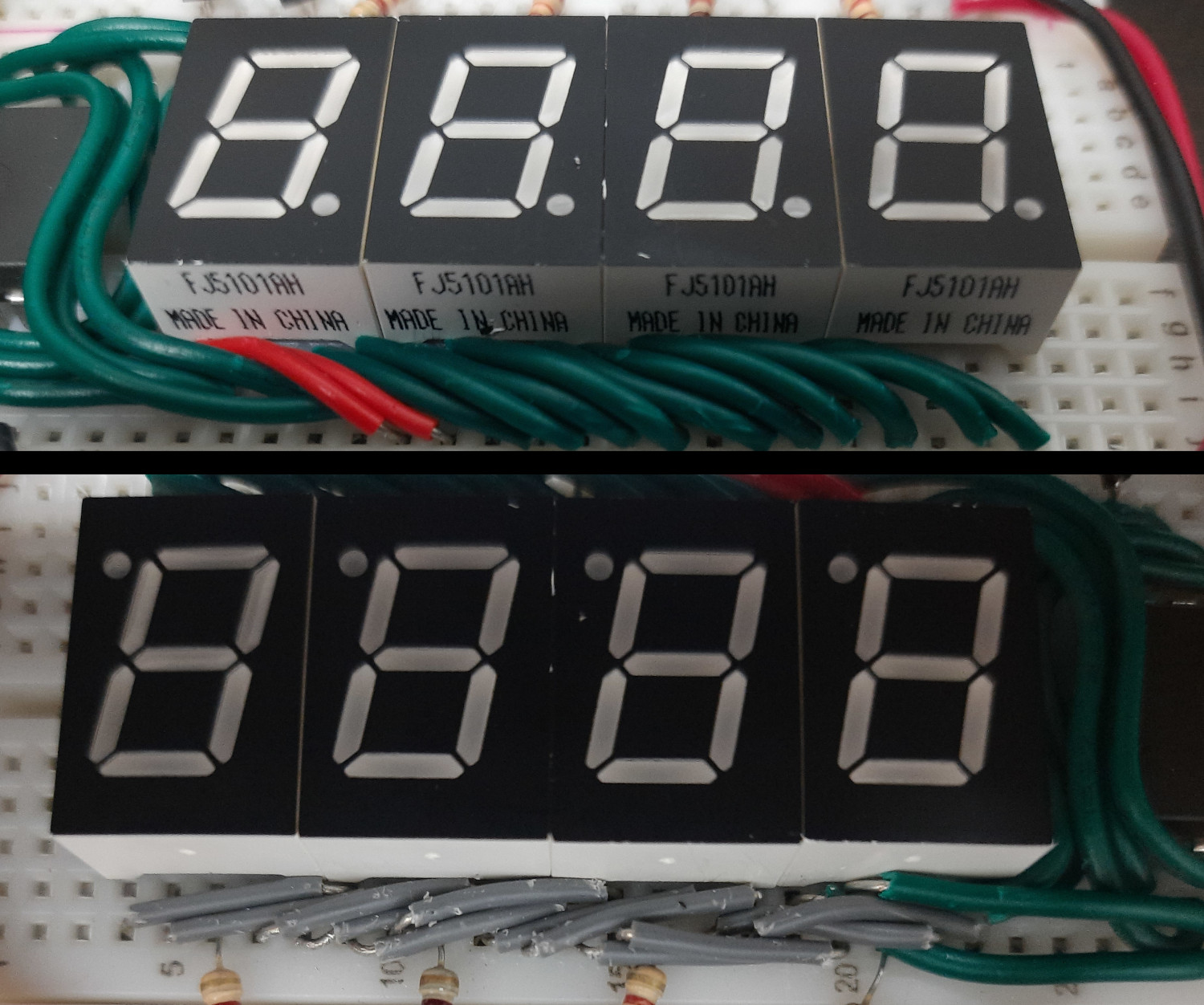
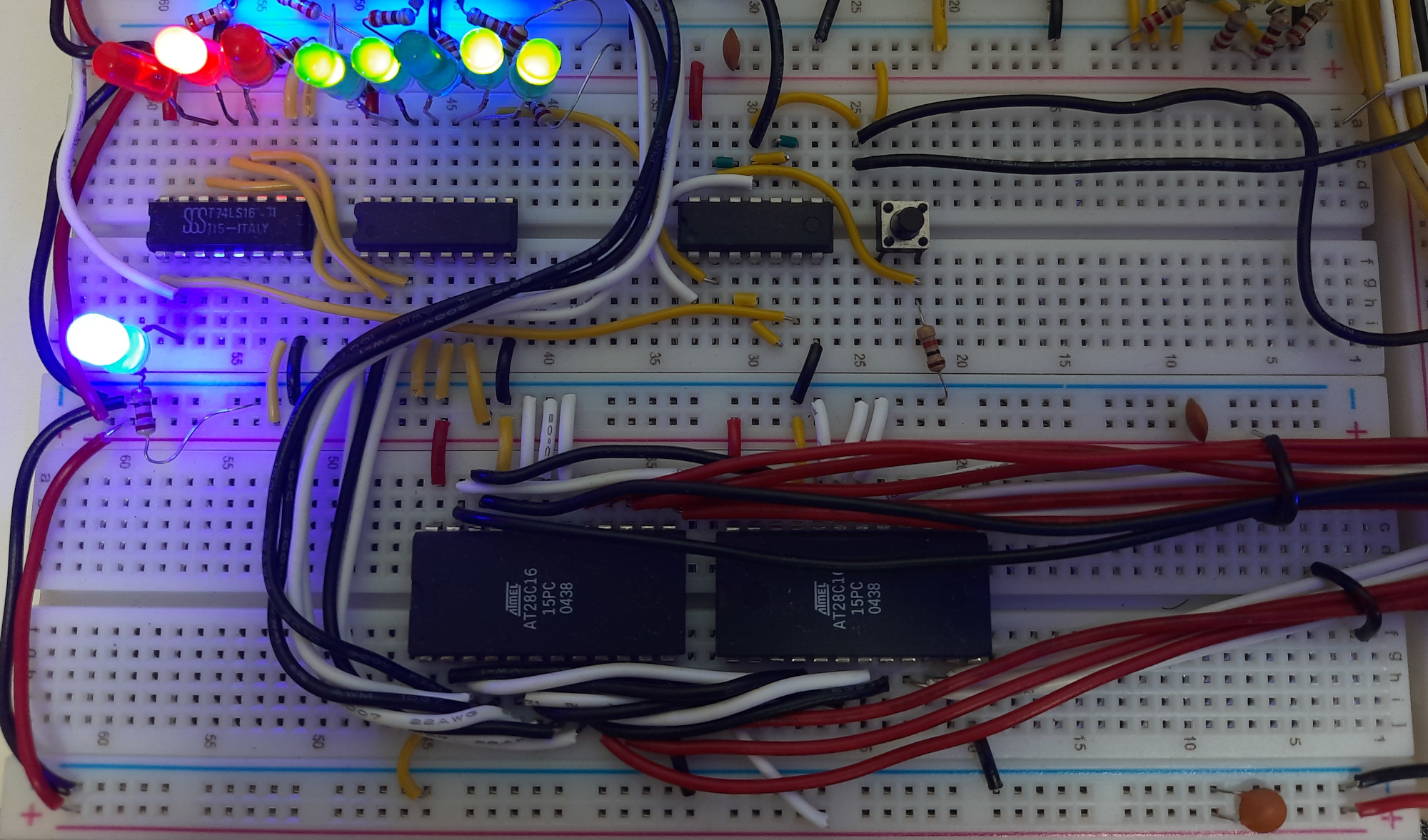
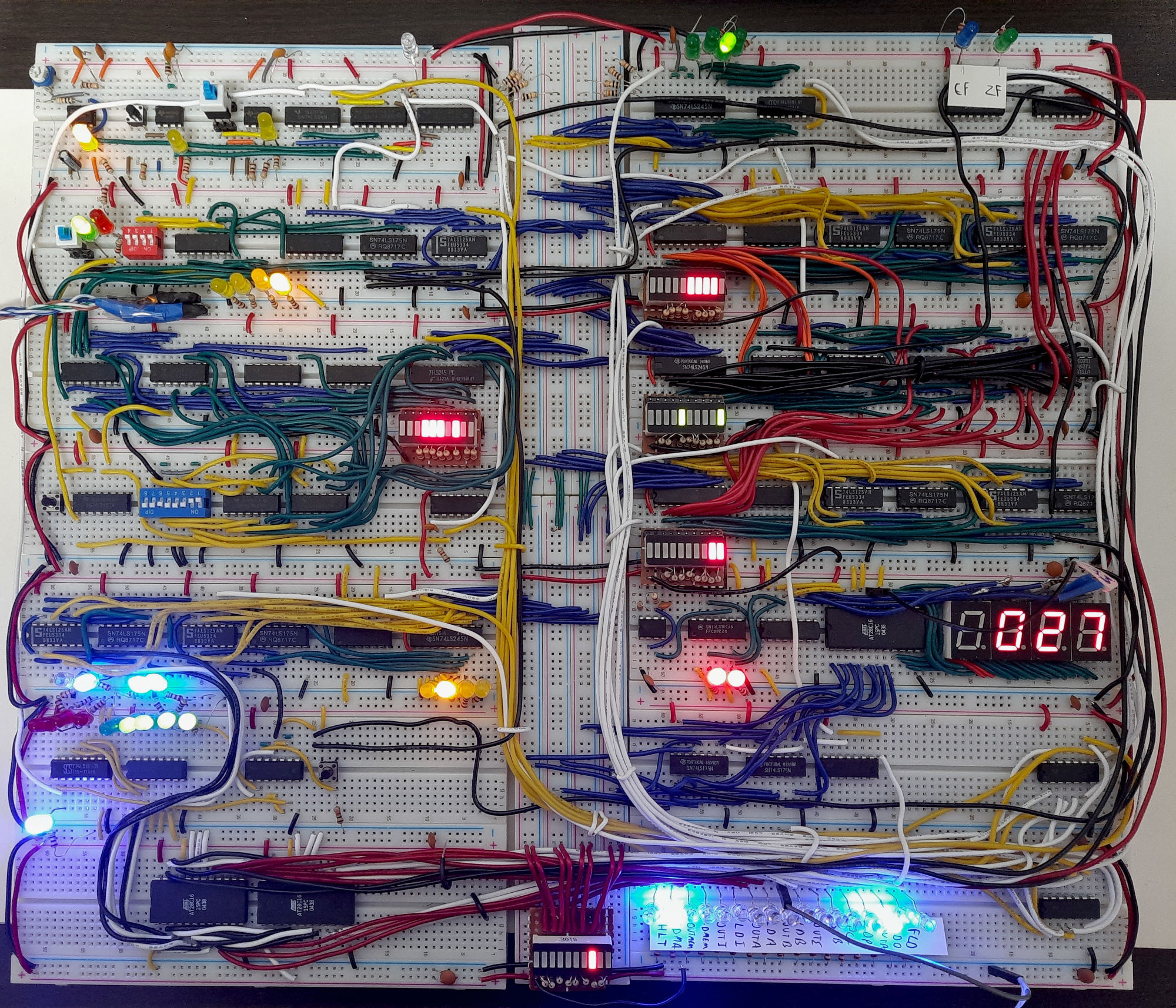
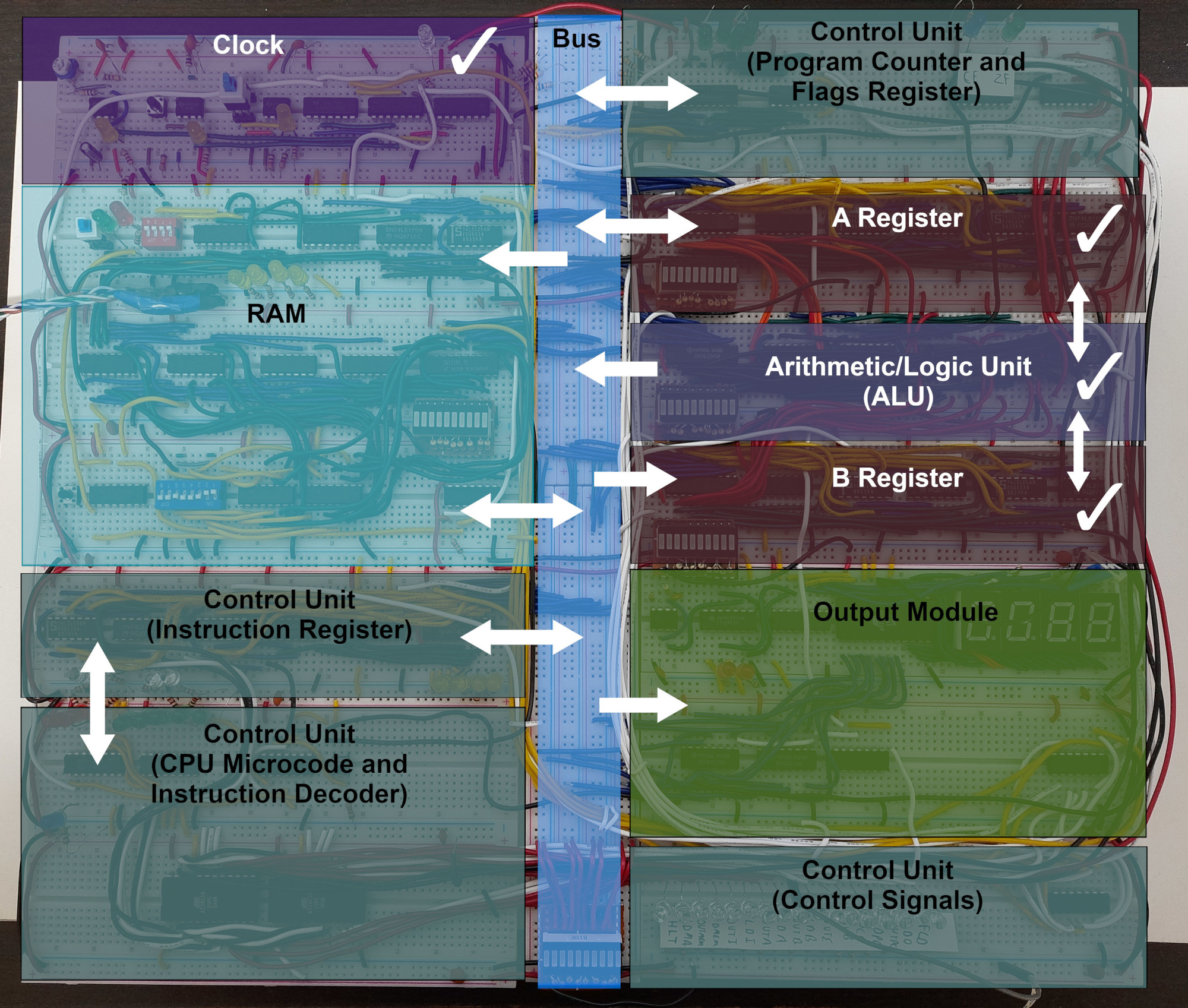
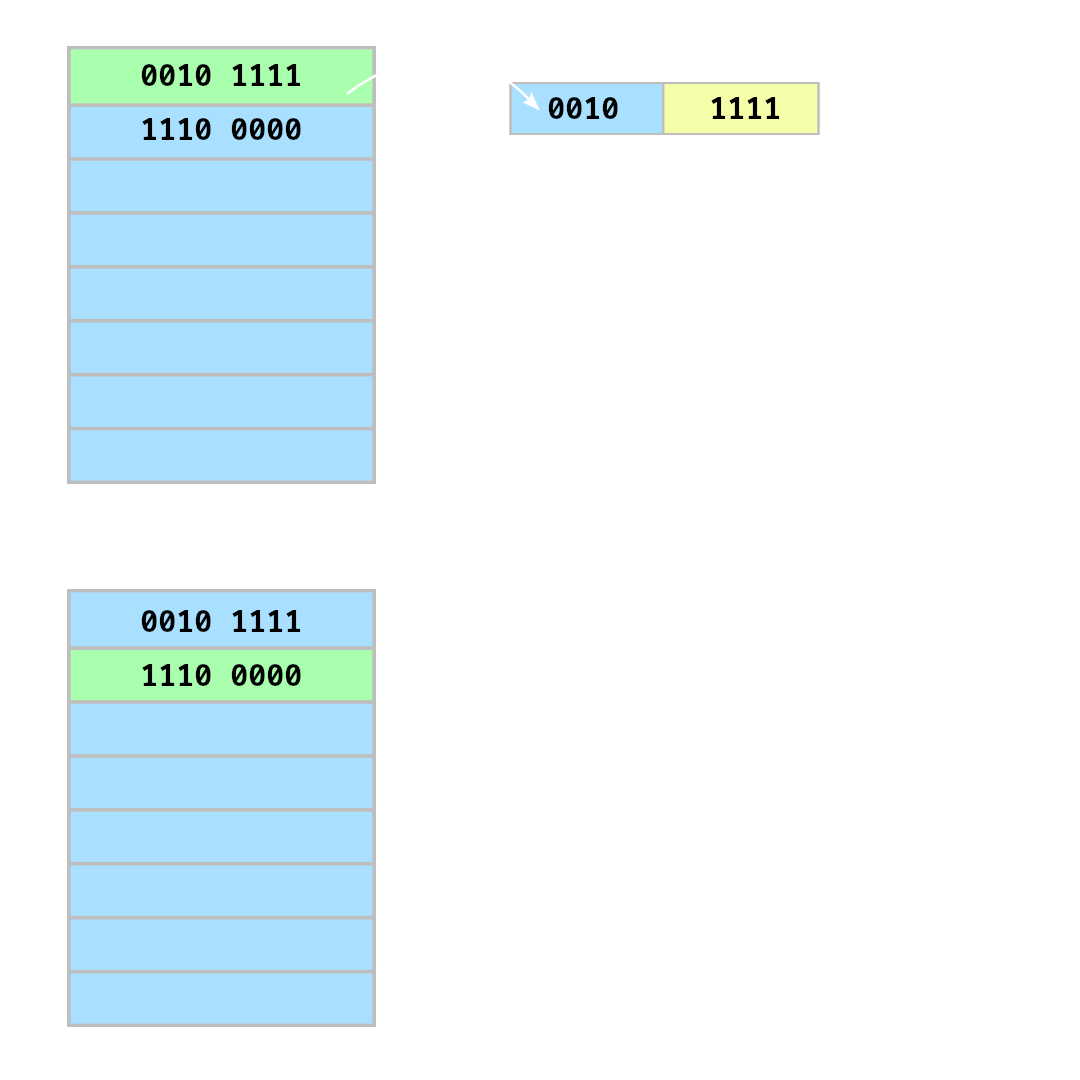
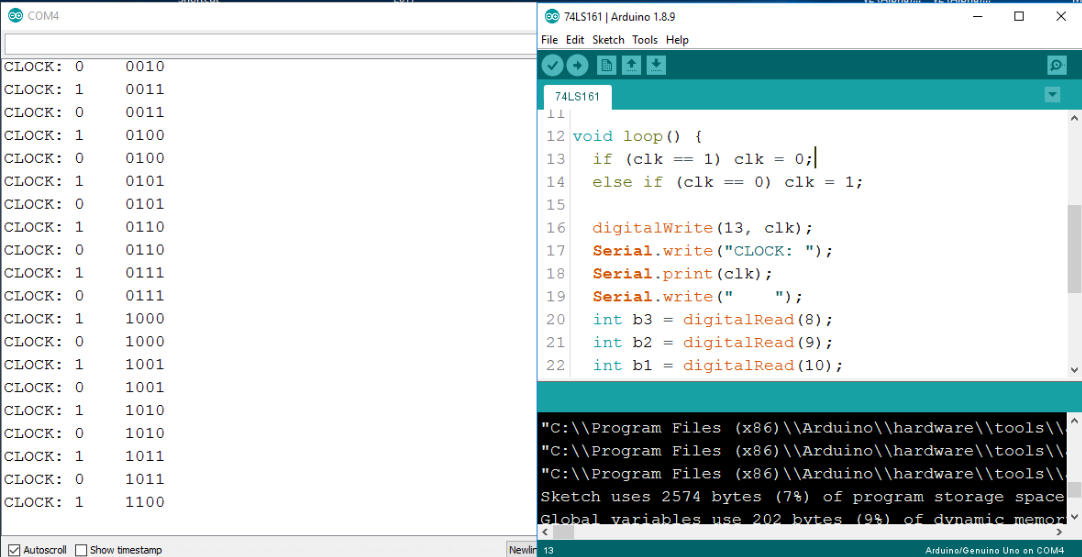
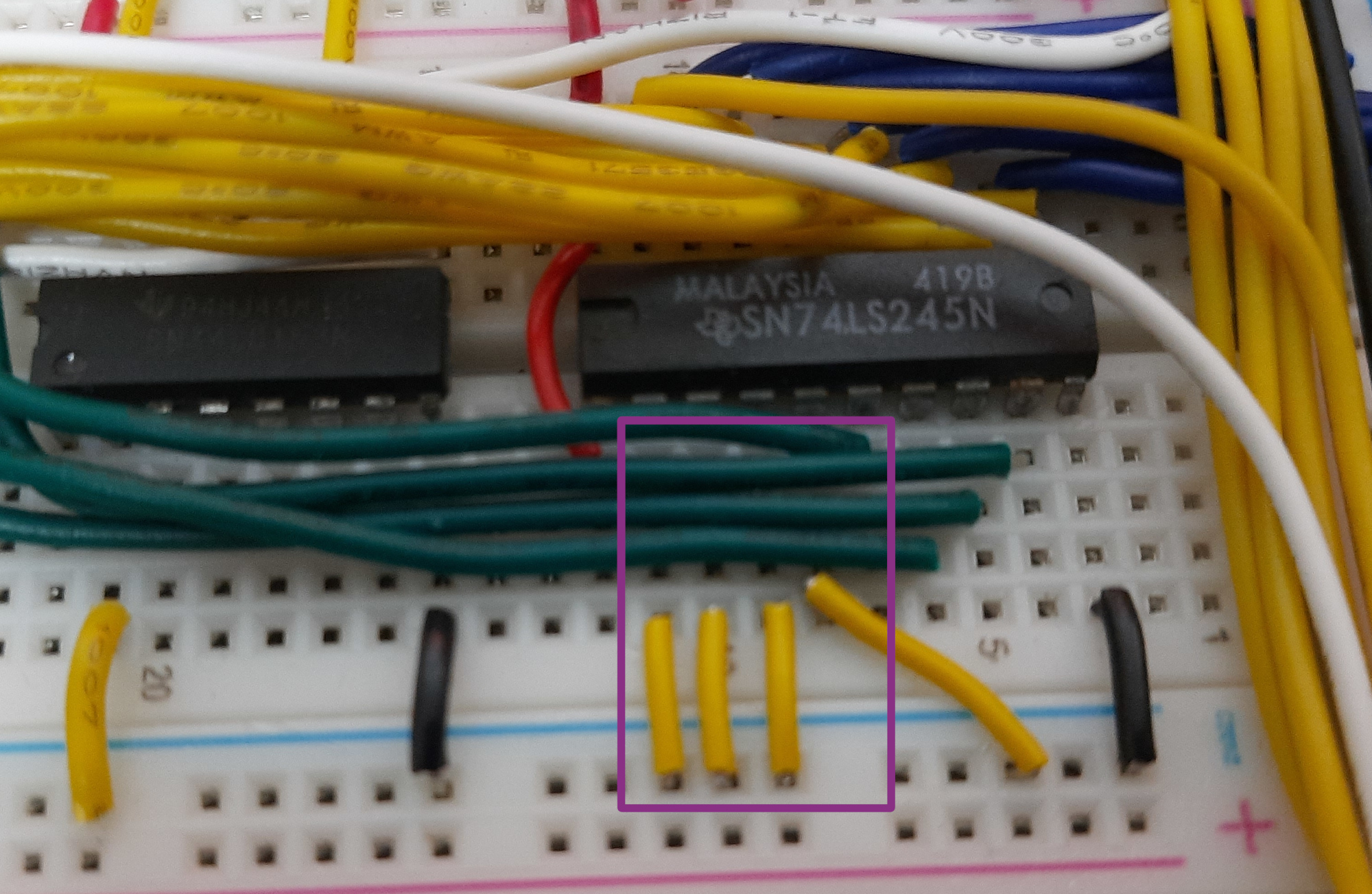
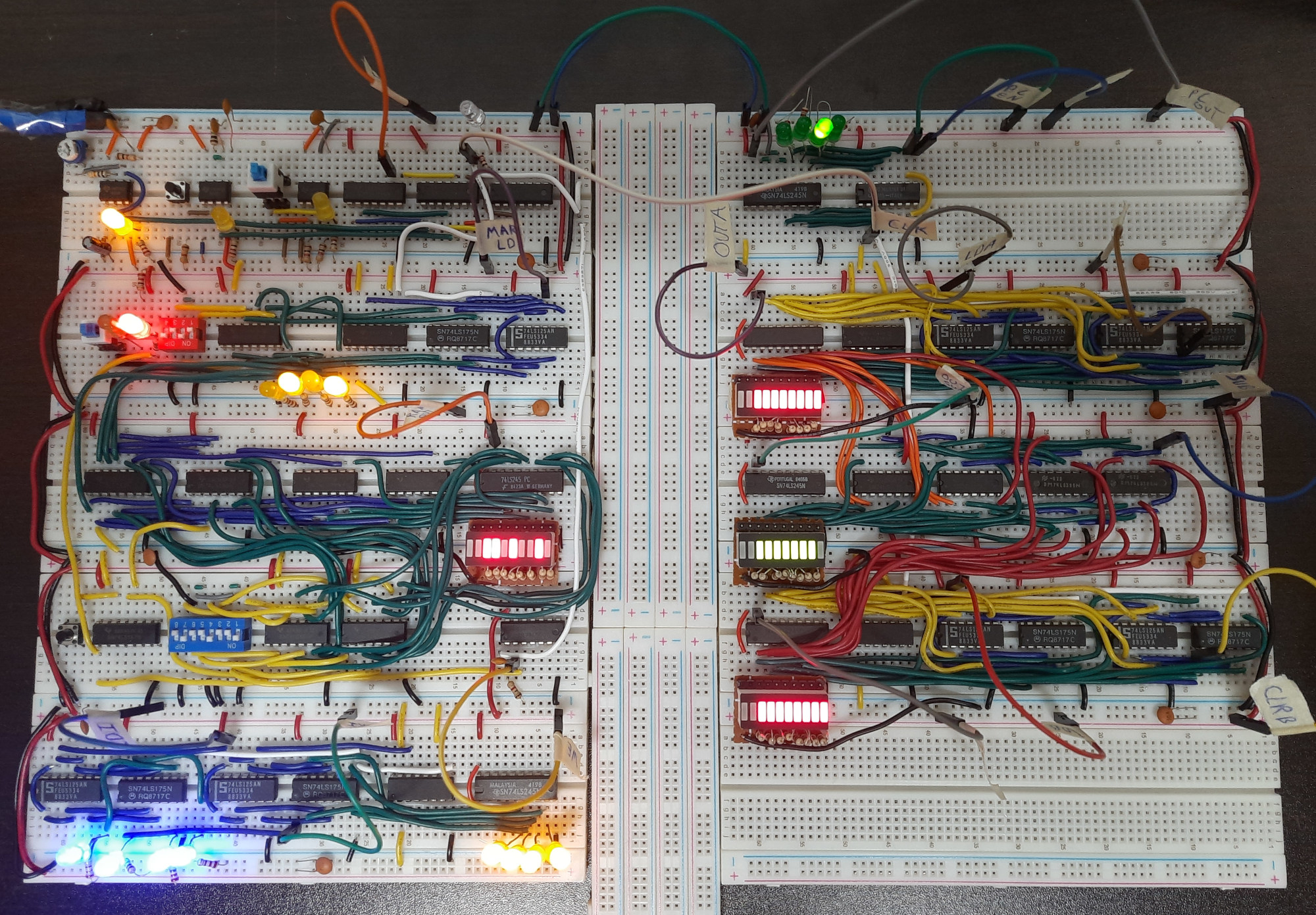
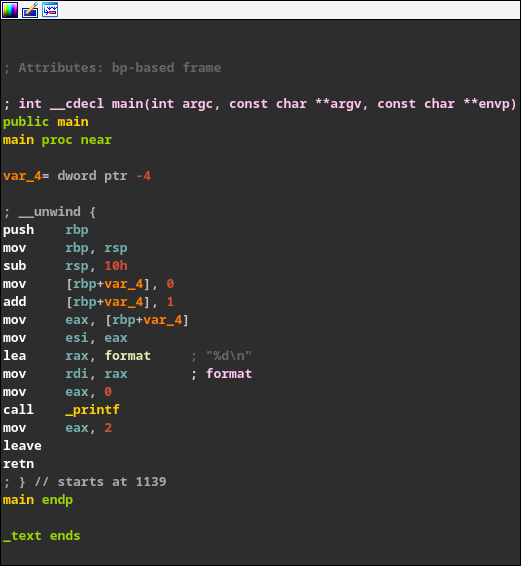
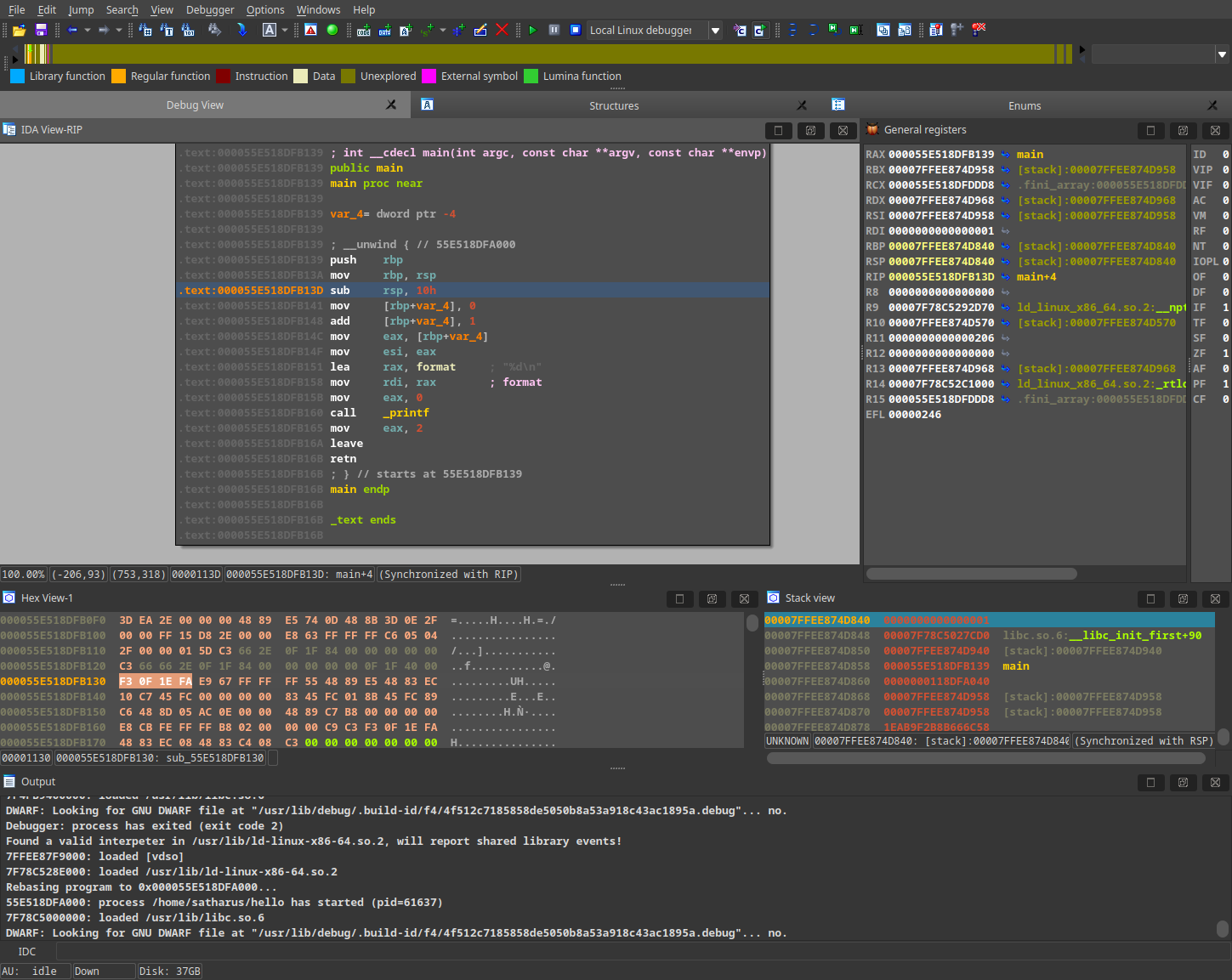
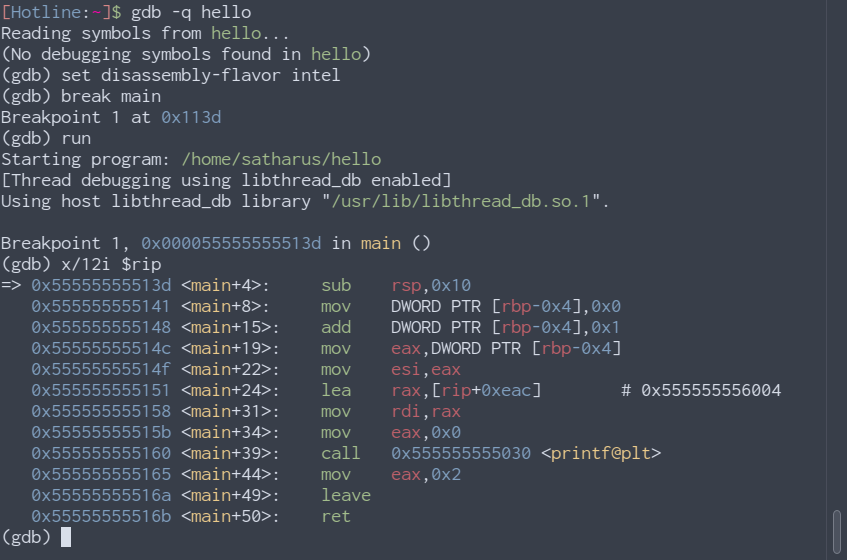
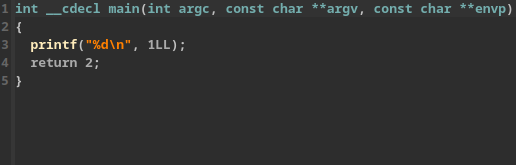
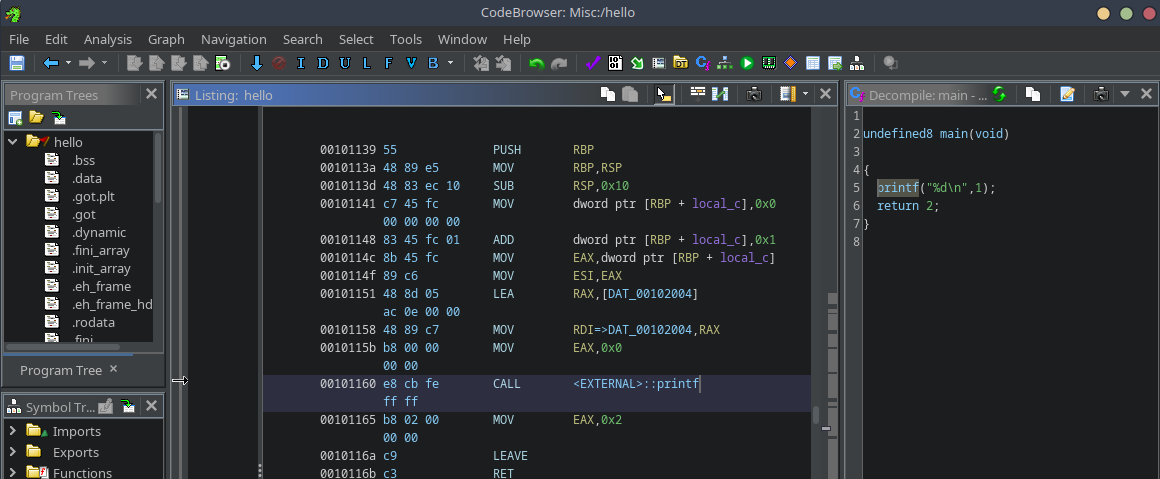
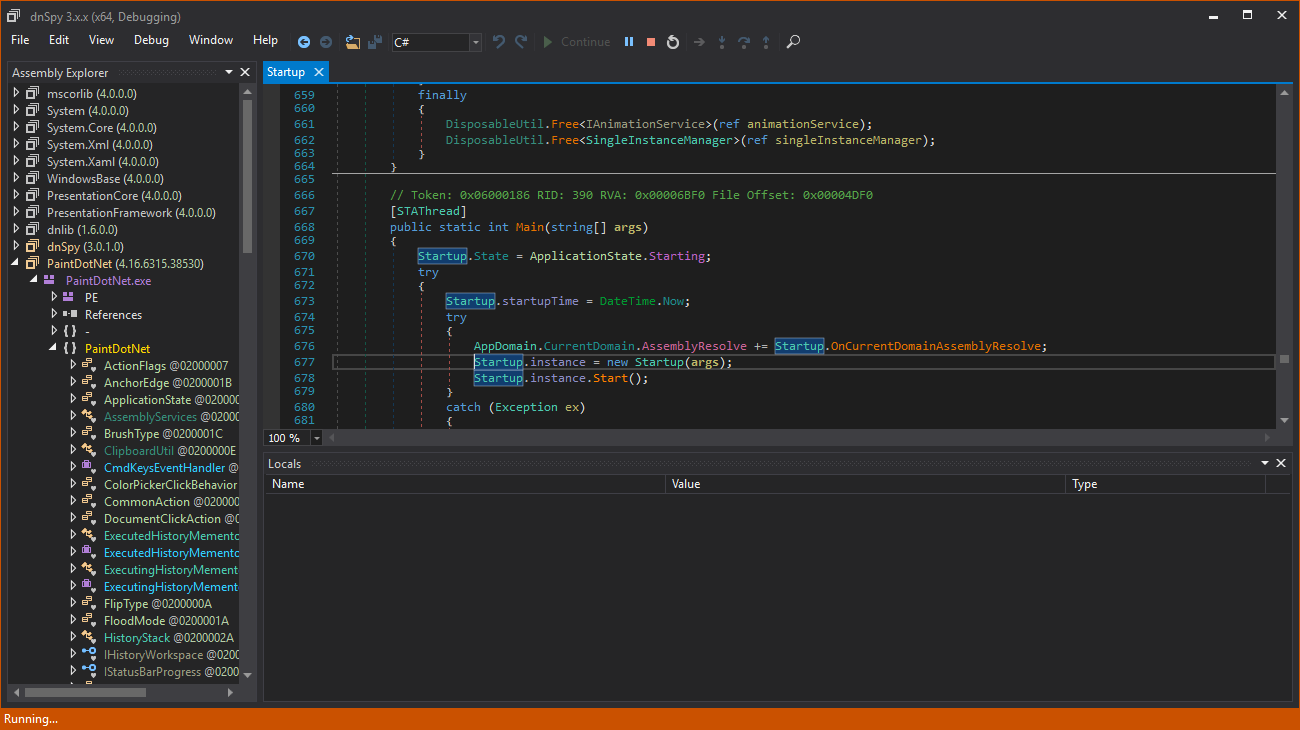
This blog started as, and still is, a way for me to share any knowledge or ideas I have with the community. Sometimes it was purely a guide such as using MASM on Linux or getting started with cybersecurity. Sometimes it would be a tutorial or an educational piece such as PowerShell deobfuscation, adversary emulation through EDR tests, or reverse engineering. Other times, it was a series on a specific topic such as the 8Bit computer build or buffer overflows. A couple of times, it was just pure banter, whether about open source, the meaning of life, or how there isn’t a specific roadmap for success. And many, many more topics.
This blog became a canvas for me to share anything and everything I wanted to share.
Experimentation
I love tinkering. I love messing around with everything and getting to know how things work. This blog gave me a chance to experiment and share my experiments with the world. Such as that time I thought of a fresh bypass for a newly-released Sysmon event. While the bypass itself is simple (and doesn’t require a blog), it connected me with many like-minded individuals with similar interests online which helped me connect more with the community and see what people at the time thought of the new Sysmon release, red-teaming strategies, and many other interesting topics. It also opened the door for me to experiment more with how Sysmon works.
Joy of Writing
Writing is fun. Or at least, in my opinion. This blog has been a side hobby for me over the years and has helped me relax many times by just writing whatever I wanted to. With the exception of 2023, I never had any pressure from myself to write regularly here. I only wrote when I felt like it. Therefore, there was no stress factor.
What Did I Gain?
Knowledge
I learnt. A lot. I learnt many things, whether while researching topic ideas, writing about topics I already knew a fair share about, researching topics I somewhat knew, or having a reader message me or comment a fun fact regarding a topic I wrote. I learnt from all of these. More importantly, I learnt more about writing and improved my communication skills and consistency.
Friends!
While this blog started originally for my inner circle and friends, I think it went beyond that and at the same time connected me with many other professionals and new friends. I got to know so many like-minded people.
Impact on the Community
It is always nice to give back. I feel that this blog, in one way or another, has given back to the community. You have no idea how happy it makes me when someone reaches out for advice or a question based on something they read on this blog. It does make me feel like I have truly given back to the community.
Giving back to the community matters because without the community, public resources, and knowledge sharing, you probably wouldn’t be where you are now. It is nice to be proud of yourself, your effort, dedication, and work, but in the end, you still have to remember those who have helped you (even indirectly), be grateful to them, and give back when you can. If you believe that you’ve succeeded completely through your own hard work and research, I have bad news for you. :)
Commitment (partially)
“The exception of 2023”… Well, this year, as you can see, I have published a blog post every month. While it may not have been easy for me to think of different ideas to write about, I managed to do it.
However, in previous years, I sometimes committed myself to getting a blog post out “in time” for a specific event or date. Overall, I saw a slight increase in my commitment skills 😃. This blog was, and still is, a way for me to commit to writing ideas I have.
People Liked It!
This blog has been acknowledged by many people in the industry. This helped me get myself out there. No one can deny that it is good for your career!
Management at previous jobs have acknowledged my writing skills by reading my blog and allowed me to write for the company’s blog even though it wasn’t my job to write at the time at all. One of the side duties I had at some point was advising the presales and marketing teams technically by helping them write. This gave me exposure to other parts of the industry which I had no idea about.
Recruiters have also read my blog and some have commented about it in my interviews over the years. This is obviously because I have it on my resume. However, if they wanted to reach it other ways they probably could.
Get Yourself Out There!
If you have any ideas or knowledge you want to share, create a blog, and post the ideas there! There are many platforms you can blog on. This includes Substack, Medium, Dev, or even LinkedIn Articles. Use whatever makes you get your ideas out there. You don’t have to know web development or create your website from scratch. Just get blogging! There is no reason to hesitate about it. Get your ideas out there and don’t let any fears hold you back. There is no such thing as a bad idea.
Epilogue
It has been five years of maintaining this blog, and I don’t mean to stop any time soon.(just pls don’t expect a blog each month next year as well thx)
Thanks for sticking throughout the journey! Here’s to five years of creativity, knowledge sharing, joy, and success 🍻. Obviously, none of this would’ve existed without any of you, my readers. Those who follow the blog, give feedback, and share it with their friends are the reason I continue doing this!
Since it started with comic books, to finish this reflection, I will share one of my favourite comic strips. Here’s to anyone who ever felt that whatever they’re doing isn’t enough or doing an impact.

The Brave and The Bold Volume 3 #30, DC Comics (Feb 2010)
Until next time, dear reader. As always, thanks for reading.
Cover image credit: Everyone on the beach by /u/RetroFreak05
]]>





 .
.